Whether your org is about to begin its journey for SOC 2, or you’re planning to wrangle up more standards (think ISO 27001, CMMC, and HIPAA, to name a few), the set of tools and software you have in place can be make-or-break. We asked our customers what their recommended tools were, and compiled your shopping list for security and privacy program essentials.
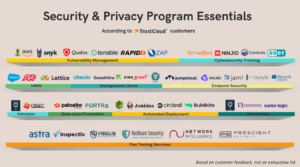
Tools or services marked with * denotes a partner or integration.
Vulnerability Management
What these tools do: help organizations identify, assess, and address vulnerabilities in their computer systems, networks, and applications. They scan for vulnerabilities, prioritize risks, provide patch management guidance, and generate reports to support effective vulnerability remediation and improve overall security posture.
Cybersecurity Training
What these tools do: provide interactive resources and educational content to improve cybersecurity awareness, knowledge, and skills. They offer training modules, simulations, assessments, and reporting to educate individuals and organizations about cybersecurity best practices and threats.
Human Resources Information System
What these tools do: automate the process of evaluating employee performance. They enable goal setting, continuous feedback, and performance tracking. These tools improve efficiency, align individual goals with organization objectives, and support the identification of areas for improvement.
Background Check
What these tools do: verify personal, professional, and criminal histories of individuals. They utilize data sources to confirm identities, validate employment and education history, conduct criminal record checks, and sometimes assess credit history. These tools enable organizations to make informed hiring decisions and mitigate potential risks.
Endpoint Security
What these tools do: protect individual devices (endpoints) such as computers, laptops, and mobile devices from various security threats. They help prevent unauthorized access, detect and block malware, enforce security policies, and provide features like firewall protection, encryption, and vulnerability scanning. Endpoint security tools aim to secure endpoints and the data they store, both on-premises and in cloud environments.
Intrusion Detection
What these tools do: monitor and analyze network traffic to detect and alert potential security breaches or unauthorized access attempts.
Data Loss Prevention
What these tools do: help prevent sensitive data from being unintentionally or maliciously leaked, both internally and externally. They monitor and control data movements, apply policies to detect and block unauthorized transfers, and encrypt or tokenize sensitive information to protect it from unauthorized access.
- Palo Alto Network
- Digital Guardian (Fortra)
Source Control
What these tools do: manage and track changes to source code and other files in software development projects. They provide features such as code collaboration, revision history, branching and merging, conflict resolution, and backup capabilities. These tools help teams work together efficiently, maintain code integrity, and facilitate easy rollback to previous versions if needed.
- This post does a great job of listing some of the most known version control tools
Automated Deployment
What these tools do: streamline the process of deploying software applications by automating various tasks involved in the deployment process. They enable the rapid, consistent, and error-free deployment of applications across different environments. These tools typically handle tasks such as building and packaging the application, configuring infrastructure, orchestrating deployment processes, and managing the release of new versions. They help improve deployment speed, reliability, and scalability while reducing manual effort and minimizing the risk of errors.
Monitoring
What these tools do: track and collect data on various aspects of a system, network, or application, providing real-time visibility and insights into performance, availability, and security.
Penetration Testing
What it is: a security assessment technique where ethical hackers simulate real-world attacks to identify vulnerabilities and weaknesses in a system or network.
TrustCloud has a pool of CPA audit firms and partners to help provide a joyfully crafted audit experience.
- Astra *
- Inspectiv*
- Fidelis Risk Advisory*
- RedTeam Security*
- Network Intelligence*
- Prescient Security*
To see their pricing, availability, and turnaround time, click here.


