The position of CISO is not an enviable one. Modern CISOs face enormous challenges like managing the complexity of on-prem and cloud environments, being responsible for the actions of thousands of employees without having authority over them, being perceived as a drag on growth and other resources, and trying to keep up in a compliance and technology landscape that just keeps changing.
Oh and budget? Limited and scrutinized.
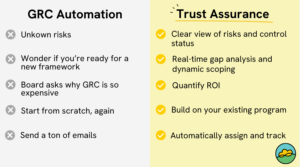
So how is a CISO to ensure their GRC program is good enough for now, the future, and every step in between? Let’s explore the concept of Trust Assurance, what a CISO needs to build Trust Assurance, and what CISOs need to get their GRC programs modernized.
Why existing compliance solutions fall short
There are many well-known compliance solutions teams can choose from, but despite their automation, they still rely on manual processes around documents, spreadsheets, and emails. Just a few of the challenges include:
- Disconnected processes relying on point-in-time snapshots lead to data gaps and siloed IT management, preventing a clear picture of overall compliance posture and risk
- Inconsistent metrics make it hard for CISOs to demonstrate program impact and ROI
- Growing list of point solutions lead to ballooning budget
- Legacy solutions are hard to integrate with new software
- Security questionnaires, risk registers, evidence collection and other projects require cross-team collaboration, but it’s extremely time consuming to communicate what is needed from whom, and track status
What is Trust Assurance?
The concept of Trust Assurance centers around adaptable, measurable confidence that the information security and privacy controls, processes, and systems across an organization are effective, predictable, and transparent. Basically, Trust Assurance is knowing and proving that your GRC bases are covered.
When an organization enlists a GRC partner that provides active real-time risk management instead of just workflow automation, it can move from a traditional reactive stance to a predictive one. Modern GRC platforms can integrate fully across an organization’s cloud environments, moving compliance efforts from a silo to an integral part of IT systems and cloud environments. Not only does this yield better results, but it eliminates processes that previously required manual oversight and led to dangerous disconnects.
Why Automation Isn’t Enough
Popular compliance automation solutions tend to rely on static information and templated processes, which creates many blind spots. It can even increase the workload of security teams, especially if organizations do not align exactly and specifically with a platform’s requirements. While automating these tasks has saved time and manual labor, it has also brought a set of new problems, and doesn’t meet the needs of more complex organizations.
Static information does not capture an organization’s dynamic needs as it grows and regulations shift. When these tools do not readily adapt to changes, the tool becomes something to work around, not with.
Key Components of a Trust Assurance Program
Wondering how to evolve your GRC program to Trust Assurance? Here are capabilities you’ll want to prioritize:
- Dashboards and reports that scale – a clear, consistent view of program status helps your prioritize projects, identify gaps, and allows CISOs present their impact to the board
- Predictive and proactive elements – You don’t need another ticketing system or alert center. Your tools should be able to identify how to remedy existing gaps and plan for upcoming needs
- Integrations with on-prem, cloud, and legacy solutions – Adding more standalone tools doesn’t address the need for a comprehensive view of control coverage, audit readiness, and more. Trust Assurance is only possible with tools that integrate with your stack, and work in both on-prem and cloud environments, and limit the need for point solutions.
How to Know Your GRC Program Is Working
Most GRC programs are short on measurable impact and outcomes. Here are six quantitative and qualitative measures you can use to assess the efficacy of your GRC program:
Quantitative:
- Reduced loss and financial liability: Streamlined compliance processes will reduce the financial losses associated with breaches, fines, non-compliance, and litigation
- Connection to revenue: Improved reporting combined with faster and more accurate security questionnaire responses show how GRC efforts are a growth vector for revenue teams
- Efficient operational spend: Automating IT risk and compliance with a trust assurance model increases operational efficiency and productivity, allowing employees to focus on innovation
Qualitative:
- Improved visibility: CISOs and those responsible for GRC programs can be confident that policies and controls are up-to-date, risks are being accurately tracked, and any gaps are known and appropriately prioritized
- Assured scalability: Risk and compliance needs only become more complex. The Trust Assurance model equips organizations with the tools and capabilities it needs to scale without significant increase in cost or resources
- Enterprise-wide security and privacy culture: The Trust Assurance model makes GRC understandable and easy to execute by integrating directly into employees’ daily workflows, and creating workflows that are easy to follow and complete
Because Trust Assurance platforms make GRC so easy to measure, the benefits quickly become clear. Trust Assurance helps turn GRC from a cost center into a profit center, empowering security teams to become more strategic, effective, and proactive.


